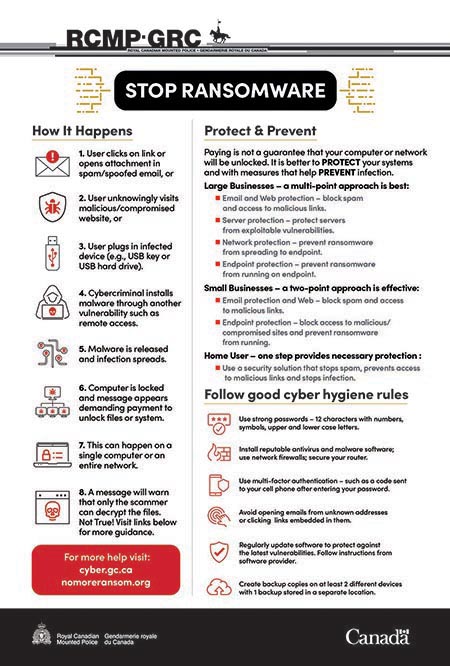
Stop ransomware
How it happens
- User clicks on link or opens attachment in spam/spoofed email, or
- User unknowingly visits malicious/compromised website, or
- User plugs in infected device (e.g., USB key or USB hard drive).
- Cybercriminal installs malware through another vulnerability such as remote access.
- Malware is released and infection spreads.
- Computer is locked and message appears demanding payment to unlock files or system.
- This can happen on a single computer or an entire network.
- A message will warn that only the scammer can decrypt the files. Not true! Visit links below for more guidance
Protect and prevent
Paying is not a guarantee that your computer or network will be unlocked. It is better to protect your systems and with measures that help prevent infection.
Large businesses - a multi-point approach is best
- Email and Web protection - block spam and access to malicious links.
- Server protection - protect servers from exploitable vulnerabilities.
- Network protection - prevent ransomware from spreading to endpoint.
- Endpoint protection - prevent ransomware from running on endpoint.
Small businesses - a two-point approach is effective
- Email protection and Web - block spam and access to malicious links.
- Endpoint protection - block access to malicious/ compromised sites and prevent ransomware from running.
Home user - one step provides necessary protection
- Use a security solution that stops spam, prevents access to malicious links and stops infection.
Follow good cyber hygiene rules
- Use strong passwords - 12 characters with numbers, symbols, upper and lower case letters.
- Install reputable antivirus and malware software; use network firewalls; secure your router.
- Use multi-factor authentication - such as a code sent to your cell phone after entering your password.
- Avoid opening emails from unknown addresses or clicking links embedded in them.
- Regularly update software to protect against the latest vulnerabilities. Follow instructions from software provider.
- Create backup copies on at least 2 different devices with 1 backup stored in a separate location.
For more help visit:
- Date modified: